You are currently browsing the tag archive for the ‘Social Network’ tag.
Tag Archive
Niche Social Platforms – Possible Fragmentation?
November 21, 2012 in Governance, Information Lifecycle Management, Social Media | Tags: Application programming interface, Dick Costolo, Facebook, Fragmentation, Google, Open, Social media, Social Network, Social Stream, Standards, Twitter, Virtual Private Network | 1 comment
Are Niche Social Media networks the future? This was a question in a recent #SWChat that I attended. Niche networks, it was explained, meant either private or bespoke networks using twitter or yammer-like platforms, although niche could be applied to any functional clone of current social platforms. While the chat concluded that this is not the face of the future, most participants expected niche alternatives to be part of it.
The reasons for this were twofold. Firstly the general preference across all industries is to maintain corporate privacy in communications other than PR and Marketing. Most companies today are gradually enabling social communications within their firewalls and seeing the benefits. However they are also reluctant to extend that capability outside the firewall unless a Virtual Private Network (VPN) has been established for connecting external parties. VPNs have overheads and rapidly become difficult to scale when the number of parties being serviced reaches into the 10,000’s.
Mass connectivity means public connectivity and so limiting exposure can only be achieved by either no connectivity or by using smaller community platforms or niche solutions.
The second reason has more to do with application access to large social platforms such as Facebook, LinkedIn, Google+ and especially Twitter. In August Twitter announced significant changes in their Application Programmable Interface (API V1.1) through which other applications like Hootsuite, Kred.ly and Sees.aw access the twitter stream. In the view of many the changes were restrictive to the point where they considered alternatives such as app.net, which originally offered Twitter-like capabilities for a flat annual fee of $50.
Both arguments drive fragmentation, one for reasons of security and the other to avoid control and restriction by the third party platform. Fragmentation will meet some of these perceived expectations but it is also likely that many of the offshoots will encounter similar challenges of scale and security, possibly even invoking similar or harsher constraints on usage. Any communication with a member of the public can find its way onto any one of the social platforms. That is the magic of digitization; scanning, OCD, cut and paste allows any thing said, signed or written to be copied. And any social platform, niche or otherwise, that offers an API will provide rules and constraints.
The biggest detriment, however, is not the fact that niche alternatives can’t fully satisfy the needs of either group. Fragmentation separates and dilutes the social stream. Additional fragmentation, possibly caused by further experimentation with security and flexibility options amongst others, further separates and dilutes the stream. Instead of access to large and global communities niche solutions will restrict social participation to those communities in which we are most comfortable. The value of the social network is diversity, immediacy and the pulse on our collective thoughts and actions. Niches can only provide a window onto the communities they serve, and these become increasingly homogenized as membership and contribution is limited to a smaller set of like-minded or similarly cultured participants.
There are alternative approaches that may reach a higher level of satisfaction for the disaffected parties.
On the enterprise side: a more comprehensive and informative set of policies around information and communication. An education program that will help internal and external participants understand the appropriate tone, content and behavior; not just the do’s and don’ts but the rationale and reasons why certain information is private and should remain so, or why good standards of behavior improve the quality and value of interactions. Establish guidelines for how to conduct research, collaboration and networking. Technology may be able to check any dialogue against policy, which is a boon for regulated industries, but for others it is far better to have employed resources aware and well-practiced at good social interaction.
Eventually enterprises might learn that applying control and security to every asset is not scalable. As digital information increases exponentially it is more effective to identify core private information and ensure security for that domain. For everything else publish in the cloud according to the comprehensive policies mentioned earlier.
On the unconstrained platform, and in particular Twitter, consider a proactive dialogue with your peers and Twitter representatives. The August announcements could have been phrased differently, they certainly did not evoke a sense of synergy between the platform and the development community. However there is little in the new requirements that isn’t reasonable other than the style in which it was delivered. Polishing the guidelines and making them requirements ensures quality and consistency. Authentication is a valid requirement to prevent easy abuse. Endpoint rate limits and user counts are reasonable statistics to conduct dialogue between Twitter and application development businesses, even though the communication did not phrase it that way, providing instead hard limits with an inference of future discussion but not necessarily expansion.
Support those requirements you agree with, and for those you have concerns about find a way to modify the requirements to something more acceptable to both parties. This is public innovation and one of the main charms and promises of Twitter. Find others who agree and can further modify the requirements. With community support and a viable approach you could engage Dick Costolo, Twitter’s CEO, to encourage progress and improvement. We could even call it the API spring.
I want Twitter to continue providing the simplest and best social media dialogue platform. It is not in my interest for niche platforms to dilute and detract from the stream that Twitter offers. Do what you can to educate, promote and support what is good about open communications, help build a set of policies and standards that improve communications and the API requirements for the platform that hosts them. If you don’t Twitter will be well and truly forked.
Related articles
The Golden Apple of Social Media
July 27, 2012 in Governance, Social Media | Tags: Business, Business Data, Business Development, Business Functions, Business Process, collaboration, Control, Governance, Internet Marketing, IT, Marketing, Ownership, Proof of Concept, Reputation, Responsibility, Social media, Social Network, Test Analysis | Leave a comment
An enterprise dilemma – who deserves the social media golden apple: Marketing, IT, Business Development?
Who should own Social? I have heard this question asked many times, and though the answers given are nearly always the same “CMO, CIO or COO“, the fact that the question continues to be asked suggests that such responses are not satisfactory. Most certainly the question is not the right question, after all who can own an adjective? As soon as you add the noun the dilemma is not as muddy but it is still far from clear. Whether its social media, content, information, stream or network we still don’t have obvious answers although some of those nouns give us clues.
The fact is that we do not know what the golden apple of social media really is. We do know that it is current, topical and massively popular. Additionally the more we engage the more we realize that “social” is a mindset, a behavior and like the big data that is produced – extreme. That last word should send a frisson of caution through any CEO or Board of Directors, enough to suggest careful consideration before any “engagement” let alone appointment of “social” responsibility.
“Social” means different things to different organizations and communities, so before delineating any bailiwick, the CEO or board must determine what “social” means to their business, their business culture and above all their customers. Customers are most important because the world of social is public, visible, and can act like litmus paper in highlighting public opinion, good or bad. Like it or not customers are going to be influenced by an enterprise’s “social” reputation. In turn customers and even the general public are going to influence business strategies and objectives to some degree. Understanding the risks, opportunities and attendant costs over time is critical input for any plan, and social engagement is no different. However with “social” any implementation is more visible, and feedback is much more immediate and amplified.
The best way to get to grips with the issues is through experience. The best way to get early experience is to perform Proof of Concepts (PoC). Notice the plurality, which is extremely relevant to “social”, because it is a behavior and an operational style, not a function or a process. PoCs allow you to apply “social” behaviors and styles to specific functions or processes within organizations. At the detailed level that might be Customer Service Problem Management, Sales Force Automation Management or it could be Asset Control Process Improvement. While these functions might not be the first in line for examination, they do illustrate that there is no division or department that presides over all the possible functions. Of course Marketing, Finance and IT are going to be involved, as they should, but the purpose of the PoC is to determine whether “social” behavior is a fit for specific parts of the business. Further analysis and possibly additional PoCs can then determine the scope and reach of “social” adoption. Some organizations will be better suited to “social” behavior, others may have to consider major organizational and or cultural changes. However the decision to adopt, in part or in totality, depends on business need and business commitment at the highest level if anything other than discrete projects are being considered.
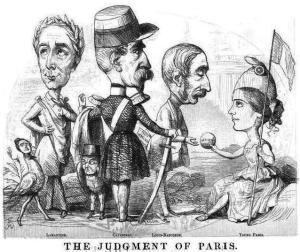
The Judgement of Paris is the myth of impossible choices. In the story Paris, a Trojan prince, was asked to present a prize of great value, a golden apple, to one of three goddesses, Aphrodite/Venus, Minerva/Athena and Hera/Juno. Paris gave the apple to Aphrodite, the most alluring and beautiful of the three, securing her appreciation and support in the future war with the Greek states. Alas he also incurred the disdain and wrath of the other two goddesses, who supported the Greek kings and princes, Agamemnon, Ulyses and Achiles in the conflict. The apple didn’t cause the war, that was Paris committing another poor judgement call by absconding with Helen, Agamemnon’s daughter, and carrying her off to be his bride in Troy. But the apple did establish which godly powers belonged in which camp during and immediately after the hostilities.
“Social Media” is a golden apple. Marketing, Finance, Business Development, Audit, Operations and IT are all potential recipients. Giving the responsibility or ownership of “social” to one of these functions is fine if the business only wants to operate “social” exclusively within that function. But here lies the dilemma in which Paris found himself, the business gains on one side but not on others. For example allowing Marketing to direct and control “social” could require the subordination of IT (I have heard that said many times) which also provides service to all other functions, their processes and their data. Is that a responsibility that Marketing really wants to be accountable for?
Paris didn’t have the option, but he could have approached Zeus, the CEO of Olympus and either given him the apple or asked him to decide. Social business is larger than any one department, it is likely that most businesses that depend on consumerism will become fully “social” both internally and externally. It therefor makes sense, once the analysis of early trials has been conducted, to create a change agent at the most senior level, reporting to the CEO or Board of Directors who is charged with developing the “Social” strategic plan and the transformation, if necessary, of the enterprise culture. Once the transformation is complete the change agent can withdraw and the functions will run themselves as they did before, they will just do so in a “social” style. In the “social” business, everyone should have a slice of the apple.
The illustration above is from an 1848 publication of the UK periodical “Punch”. The cartoon refers to the famous myth and depicts the political dilemma faced by French voters in the 1848 French General Election. It is easier to compare business departments to politicians than it is to enchanting immortals.
Curation – Amplifier or Condenser?
July 19, 2012 in Curation, Information Lifecycle Management, Social Media | Tags: browsing, Content, Curation, Data Mining, Definition, Information Lifecyle Management, Marketing, Networking, Pinterest, poll, Sharing, Signal, Social media, Social Network, Streams, visit | 24 comments
In a very short time curation has evolved from a minor supporting role to a major or even leading role in Social Media engagement. It is no longer sufficient to just share items of interest, breaking news and opinion, not if you want to be regarded as authentic and taken seriously.
Curation has many definitions, including my own: “Curation is the acquisition, evaluation, augmentation, exhibition, disposition and maintenance of digital information, usually centered around a specific topic or theme”. The Digital Curation Center (DCC) in the United Kingdom puts it more succinctly
Digital curation, broadly interpreted, is about maintaining and adding value to a trusted body of digital information for current and future use. (DCC)
Both definitions infer an information lifecyle process, that manages the digital objects from creation to deletion. Both suggest that capturing and adding value, whether by commentary or related material, is vital to the end product which is knowledge or information that can be referenced now and in the future.
However the evolution of digital curation is experiencing some fragmentation. Not that this is bad, but it does suggest the differences should be understood as curation tools will differ in features and capabilities as each tries to satisfy its target customer base. So far I have identified 3 major distinctions in curation:
- Marketing Content: comes in several forms as marketeers move away from landing pages on Facebook and web sites, and seek to amplify brand presence through curated content.
- Information (or Knowledge Content): More focused on collecting and condensing information to support a topic or subject. Most commonly a reference site usually set up for either internal or external collaboration
- Personal Content – less dependent on content management features and capabilites: can either be used for amplification (self-branding) or condensing (information).
The question I would like to pose is who visits these curated sites and what are their preferences. The following poll offers choices in the style and content of curated sites. Please let me know which sites you prefer to access for either information or shareable content. I have made a further distinction for sites that are the result of either employee or community collaboration as they possibly differ from information sites in the degree of social participation (ie more social).
SoMe Assistance in Understanding Social Media Data
June 27, 2012 in Curation, Social Media, Technology Tools | Tags: BigData, collaboration, Comprehension, Curation, Data Capture, Distraction, Filtering, Google, Internet, Meaning, Microsoft, Mobile, Pearltrees, Search Engine Optimization, SeeSaw, Social media, Social Network, Twitter, Understanding, Workspace | Leave a comment
 In a previous post I presented the challenges involved in deriving value from Big Data and in particular unstructured Big Data, which increasingly dominates the Social sphere. The tools that will enable us to make sense of the plethora of conversations, contributions and observations are still in their infancy and the likelihood that we will have to rely on human scanning and analysis for the short to mid term appears inevitable.
In a previous post I presented the challenges involved in deriving value from Big Data and in particular unstructured Big Data, which increasingly dominates the Social sphere. The tools that will enable us to make sense of the plethora of conversations, contributions and observations are still in their infancy and the likelihood that we will have to rely on human scanning and analysis for the short to mid term appears inevitable.
In his book, “The Shallows“, about the effect of the internet on our brains, author Nicholas Carr discusses the demands on our working memory or, as he puts it, “our mind’s scratch pad”. Working memory is our CPU and the agent that identifies and transfers information to our long term memory, which is our data store. It is therefore a pivotal component in our ability to seek out and retain knowledge.
“The information flowing into our working memory at any given moment is called our “cognitive load“. When the load exceeds our mind’s ability to store and process the information… we are unable to retain the information or to draw connections with the information already stored in our long-term memory”
The internet and particularly the social web is constantly bombarding our working memory with stimuli that are intentionally distracting (this post is a representational example with multiple hypertext links in the first two paragraphs). The pervasiveness of mobile connectivity means that we are always on-line, and never at rest from the interrupting nature of the medium. This suggests we need assistance in processing the social media stream, firstly in being able to recognize important and relevant information, and secondly to earmark that information for further analysis, refinement or augmentation. The first requirement is for a social media radar, the second for a social information refinery.
Search remains our favorite tool that we use to seek out information. Google dominates with 4.7 billion searches a day, but Twitter is not far behind (considering its size) at 1.6 billion, and both services are growing fast (Google at 30% increase per year – Twitter at 50% per year). However there are certain limitations in both search functions evidenced by the changes announced by both companies in the past 12 months. Google has recognized the effects of Search Engine Optimization and the fact that we demand results that are more contemporary. Both companies have added semantic search elements to their armory, an acknowledgement that searches need to be relevant to time, location, context and searcher’s intent. However such elements are far from comprehensive. Furthermore because the definitions, rules and algorithms are unpublished the searcher is dependent on Google’s and Twitter’s interpretation of what was intended. We are still a code generation or two away from being able to parametrize semantic search using our personal or group definitions and meanings.
 Turning now to the need for refinement, which is the ability to analyze what we have found, understand its value and relationship to other captured information, and to provide single or collaborative commentary on the discovery itself. Once again the technology has provided some rudimentary tools, commonly called curation tools. Related to museum curation, these tools capture and display information of interest. There are over 40 such applications and each provides a web page in which curators can display their captured content. In many cases the tools allow for comments to be added as separate components, listed in historic order with the most recent first. Some curation tools, such as Pearltrees, support content linking, allowing curators to provide insight into relationships between islands of information. Many tools provide a browser add-on that will enable the curator to save browsed/searched content to the curated web site. The tools are improving but there is still a small disconnect between the radar and the refinery functions.
Turning now to the need for refinement, which is the ability to analyze what we have found, understand its value and relationship to other captured information, and to provide single or collaborative commentary on the discovery itself. Once again the technology has provided some rudimentary tools, commonly called curation tools. Related to museum curation, these tools capture and display information of interest. There are over 40 such applications and each provides a web page in which curators can display their captured content. In many cases the tools allow for comments to be added as separate components, listed in historic order with the most recent first. Some curation tools, such as Pearltrees, support content linking, allowing curators to provide insight into relationships between islands of information. Many tools provide a browser add-on that will enable the curator to save browsed/searched content to the curated web site. The tools are improving but there is still a small disconnect between the radar and the refinery functions.
Until now. SeeSaw is still a fledgling product yet it offers to bridge that gap between scanning and curation, and holds great promise in being able to map content relevancy and provide a lens on both active streams and refined content. What is particularly appealing about SeeSaw is that it is built for visual scanning. as opposed to lexical scanning. “See”, the radar component of the tool, filters live social media streams and displays the visual content of links and embedded graphics. For Twitter this is a vast improvement on current viewing dashboards such as Hootsuite and Tweetchat. where speed reading is essential in keeping up with fast moving activities and events such as chatrooms. SeeSaw not only displays the images but can also stream the video links within individual messages.
This visual facility has three immediate advantages. Firstly the participant can remain in the chat stream without having to hyperlink to a new page, which has been a major distraction and an extended opportunity for further interruptions and distractions. Staying in the same window enables continuous contact with the flow of active conversations. Secondly it enables the viewer to see trends within the stream, connections (ie who is talking to whom) and tangential conversations. Thirdly, and most importantly, it enables the participant to save active content in the stream to the Saw side of the product, and the bridge to the product’s curation functionality. A simple toggle button allows the reader to change between the active stream (See Board) and the curated site (Saw Board). In practice this allows the participant to remain in contact and context with the conversation, as opposed to the multi-windowed, heavy interrupt laden environment to which we have been constrained. Reflection and analysis can now occur after the scan or chat, ensuring that focus and attention can be appropriately applied to both.
SeeSaw is more than welcome to my active toolkit, it allows me to “Embrace, Extend and Expand” (via EMC, via Microsoft) my social media environment. It is more than a helpmate – it has the potential to be my primary Social Media Assistant.
- At last, science explains why there are Internet trolls [infographic] (betanews.com)
- Working Memory and the Classroom (my.psychologytoday.com)
- 40 Social Media Curation Sites and Tools (socialmediapearls.com)
- The Age of Relevance (techcrunch.com)
Understanding Big Data
June 12, 2012 in Big Data | Tags: Analysis, BigData, collaboration, Curation, Data Definition, Data model, ILM, Knowledge, Knowledge Management, Lifecycle Management, Meaning, Networking, Open Source, Peter Drucker, Semantics, Social media, Social Media Value, Social Network, Tony Walker, Unstructured data | Leave a comment
 The more we know the less we understand. Nowhere is this more true than on the Social Network, where volume, velocity, volatility and variability are increasing on a daily basis. Those 4 V’s are part of a definition of big data, which includes both structured and unstructured data. We may have a reasonable chance of obtaining valuable information from the structured data population. That depends, of course, on the extremity of any single one or combination of the 4 Vs, yet author, time stamp, location or any other tag that accompanies a communication is easily identifiable. Howerver unstructured data poses a challenge several orders of magnitude greater. Structured data benefits from data models, data definitions and rules that enable us to extract reports and analyses even to the point of discovering new relationships and information from the regimented data. To do so, we need to nurture and maintain these structures, to prevent a degradation of data quality and avoid conflicts and loss, a goal that often eludes the best efforts even in mature IT shops. However this is not the case for unstructured data.
The more we know the less we understand. Nowhere is this more true than on the Social Network, where volume, velocity, volatility and variability are increasing on a daily basis. Those 4 V’s are part of a definition of big data, which includes both structured and unstructured data. We may have a reasonable chance of obtaining valuable information from the structured data population. That depends, of course, on the extremity of any single one or combination of the 4 Vs, yet author, time stamp, location or any other tag that accompanies a communication is easily identifiable. Howerver unstructured data poses a challenge several orders of magnitude greater. Structured data benefits from data models, data definitions and rules that enable us to extract reports and analyses even to the point of discovering new relationships and information from the regimented data. To do so, we need to nurture and maintain these structures, to prevent a degradation of data quality and avoid conflicts and loss, a goal that often eludes the best efforts even in mature IT shops. However this is not the case for unstructured data.
In general there are no data models, no data definitions, no rules and no discipline of housekeeping for unstructured data in Social Media. At least nothing that is commonly held. Individually, of course, we have an idea of what we are communicating, and we probably use both our own data definitions as well as those we assume are being used by others in any conversation; but these are amorphous concepts and certainly nothing that can be referenced by others or by cyber analysis. The same is true to a lesser degree in IT organizations and the worlds behind the firewalls. At least in those environments best practices such as change management and planned organization of unstructured data (viz Sharepoint) should ensure some semblance of control and order if not insights into hidden information.
We do however have some rudimentary tools at our disposal, but like early man our technical bows and arrows are a poor match against the stampeding herd of beasts that is the social network stream. So like our ancient ancestors we have to develop strategies and skills that help us survive and thrive in this world of pervasive communications. Tony Wagner, author of “The Global Achievement Gap” identified three such skills that he believes are fundamental for us to foster and teach. He calls them the “three C’s – critical thinking, effective oral and written communication, and collaboration.” He also believes that this should be the prime focus of our educators, and that we should establish “a new National Education Academy, modeled after our military academies, to raise the status of the profession and to support the R and D that is essential for reinventing teaching, learning and assessment.”
Knowing how to perform the three C’s is therefor one of the keys to success. Being able to put this knowledge into practice, and bring organization and governance to bear on the resources and data requires additional skills if enterprises plan to approach and consume the labor and thoughts of distributed social resources.
Taking these observations a little further I believe the following 5 components are necessary in order to navigate, participate and collaborate in world of social information.
1. Understanding – we need a better understanding of what we are dealing with in the social media so that we can properly distinguish and farm target crops whether they are preferences, demographics, opinions, gossip, information, knowledge, wisdom. or something altogether different. However to improve that comprehension we need to be more aware of the dynamics of how we think, analyze, and communicate effectively. What, for example, is a thought, and what are the attributes of thought that make it consumable? We have a notion of answers to those questions but they are personal and subjective. Yet we cannot rely solely on subjective interpretation, so we need a shared and objective framework or model of knowledge. Knowledge is the loadstone of the social community, and the more we understand it, its nature, behaviors and properties the more we can improve the discovery, sharing and use of valued information in the social stream.
Peter Drucker(1909-2005), one of the most respected commentators on management theory and practice, believed that “knowledge worker productivity” would be the next frontier of management. Drucker was also famous for his quote “If you can’t measure it, you can’t manage it”, to which I would add the following prefix, “f you cant understand it, you can’t measure it.” Building a common understanding and framework(s) for knowledge management is essential in determining meaning, relevancy, relationship or other characteristics of information within contextual and cultural settings. We need to be able to detect when ambiguities and obfuscations are intended and make a documented judgement on meaning when they are not.
2. Networking – it might be stating the obvious to point out that people, individually and collectively, lie at the heart of the global social community. And it stands to reason that knowing who is who, and what they know is another fundamental layer needed for success. The size and complexity of big social data demands a superior set of skills that can identify, analyze, classify and then connect individuals to each other and their knowledge sets. I described this in my previous post Network Weavers which attempted to define the needed attributes (acquisition: filtration/review: association: curation: construction). As the dimensions of the network, the participants and their contributions grow so will the level of skills, and proficient network weavers will become more of a premium resource than they are today. It is likely that networkers will depend on directories, personal or even corporate at first, but increasingly the directories will become more public and entries will contain more social information such as skills, contributions, preferences and factors that others will be able to use to determine relevancy and fit for purpose.
3. Analytics -With improved understanding of knowledge and how we use and abuse it, we can approach analysis with a higher level of confidence in the accuracy of our observations. There are techniques and technologies that attempt to extract meaning from unstructured data but they still fall short of the human computer that is the brain when it comes to analyzing written and visual communications. As with humans machine semantics are bounded by self imposed rules and definitions, and like humans, communication is improved if there is an agreed set between participating bodies. If those rules and definitions remain hidden and obscured then the output can only be regarded as personal opinion. Rating the relevancy or social worthiness of an individual or entity against undisclosed rules and definitions has as much value as the street corner tipster who whispers a sure fire winner for any given horse race. Consequently social media demands semantic definitions that are shared amongst correspondents and a semantic analysis engine with the flexibility to parametrize selected characteristics so that relevancy can be tuned to group or community objectives.
4. Curation – In an earlier post, Curation – In Need of a Cure I raised the need for knowledge workers to approach the care and maintenance of Social Media information in the same way that enterprises manage their data through Information Lifecycle Management. It is not enough just to store knowledge as we do currently with Pinterest, Tumblr, scoop.it and others: beyond catching the item in our personal butterfly net, our efforts resemble little more than childhood scrapbooks of things that caught our interest and appetites. Curation is an excellent term for the housekeeping that needs to be performed on the captured knowledge data. In museums and art galleries curation is a highly sophisticated skill set that seeks to first isolate the item of knowledge, then to expand it with information about its provenance (where it came from) and pedigree (eg what school of thought), augment it with related content (supporting and detracting) and finally exhibit it to educate and edify an interested audience. Curation is an essential component in building a rich and relevant knowledge base, and can and often does lead to new insights and innovations.
5. Collaboration – Unlike “Field of Dreams” you can’t just build a field and expect the games to begin. All the understanding, networking, analyzing and curating will bring but small value if you keep it all to yourself. The key to success lies in participation. The more you contribute, the greater value you generate both for yourself and for your correspondents. The root of the word collaboration is “labor” , meaning work or effort, and the prefix “Co” means sharing. The more you share and contribute the more you will be rewarded by your involvement with the social network. You will be further rewarded as others do the same, whether its contributing common rules and definitions, understanding of knowledge and thought, the names and skills of great social network participants, or exemplary curation of well defined and related content. It is the act of collaboration that provides the secret sauce of success and bridges the resources and knowledge in the social stream. This is not theory: this is proven without any shadow of doubt by the open source community. If you get the opportunity, interact with an open source contributor, and ask them for guidance; they have been doing it effectively, efficiently and profitably for more than a decade.
WARNING: Please don’t attempt any of the steps above without clear and careful planning
Related articles
- Search is Not Enough: Using Solr for Analytics (architects.dzone.com)
- Examples to help clarify what’s unstructured data and what’s structured? (parasdoshi.com)
- Tackling that unstructured data mess, practically (infocus.emc.com)
- Visualising The Future – New Techniques will revolutionise understanding and interpretation of ‘big data’ (blog.bt.com)
Introduction to Opencollaborarchy
February 17, 2012 in Big Data, Curation, Frameworks, Information Lifecycle Management, Social Media, Technology Tools | Tags: Architecture, collaboration, Marketing, Open, Social media, Social Network | Leave a comment
It takes about 6 months of immersion and splashing about in the waters of Social Media to feel comfortable and confident enough to not just tread water but make strokes that might lead to reaching one of the other sides. That is of course if any of the other sides are visible, as the social network is far larger than any public amenity previously encountered by a an order of magnitude. For those about to jump in for the first time – do not be afraid – the temperature is fine and its predominantly shallow water. You wont get into difficulties and the worst thing that can happen is a little bit of personal embarrassment, but then nobody is really watching that closely.
During those months of familiarization, learning how to engage with Facebook, posting to your wall, writing up your “resume on steroids” aka Linkedin, pinning your curated content on Pinterest or taking the bolder step of blogging or tweeting you may have wondered a little bit about this medium, the proximity of millions of people all swimming about much the same as you. What is it? Rushing through the list of possible descriptors it’s a club, a hangout, its a place to share your thoughts and life with friends , it’s a knowledge pool, it’s the maker and breaker of news. it’s the university of life, the crucible of change even revolution, it’s a marketing paradise. Finally a reliable source on how commercial brands can track the public success of and reaction to their products and identity. And that is how it is viewed today. At a recent Social Media Week event in New York the main topic of conversation was how to use the social network for competitive advantage, with the focus almost exclusively on the marketing advantage. One of the biggest discussions of the week was who owned Social Media – marketing or PR, and ancillary to that was the often expressed sentiment that CMOs owned Social Media and the strategy around it. Furthermore that ownership and the technical budget that accompanies it indicates that the CIO should now report to the CMO.
But before anyone stakes a claim on Social Media, shouldn’t we first understand more about Social Media, what it is, how it is structured (or non-structured) and what are the economics of the model(s), who are the principle players, what are the constituent parts, and what are the appropriate standards and rights that should attend the use and access to this massive data universe. And the questions do not end here. Most importantly what is the value of the Social Network to the individual, the private citizen, the corporate or public sector employee, the community, the enterprise, the nation, mankind? Without doubt it is worth far more than the sum of its parts, but the largest opportunity of all lies in collaboration. Being able to reach out and share is the fundamental behavior of the social network, and millions upon millions of people do so every day. They participate, contribute and collaborate freely and willingly, and it is manna from heaven for the marketing profession, who understandably have sharpened their knives to capture the likes and dislikes of the masses. But if that energy and effort is properly channeled, if tasks can be performed by social network teams, if thoughts and ideas can be evolved and extended to stimulate innovation then marketing will be just the tip of the value iceberg.
In the end no-one can or should own the social network, money will be made from it, reputations will be won or lost, but ultimately the social network benefits and belongs to all of us, to Everyman. We are all contributors, we are all curators, we are all custodians, and our first task as stewards is to define and describe the infant that is our charge, so that we may nurture and care for its health and growth. This blog will attempt to start that process, and with a lot of help from others (both a plea and an invitation) hope to bring some focus and understanding to the ever expanding pool of knowledge and resource that is the social network.
.
Related articles
- Extreme Social: Social Media and The Power of Social Networks (michellegilstrap.wordpress.com)











Curation – in Need of a Cure?
May 15, 2012 in Curation, Information Lifecycle Management | Tags: Attribution, Brian Solis, British Museum, collaboration, commentary, Content, Curation, Curator, Data Administration, disposition, evaluation, exhibition, Information Lifecyle Management, Management, Network Weaver, Openness, organization, Pinterest, scoop.it, Social media, Social Network, Transparency | 3 comments
Photo from New Exhibit! Native American Cultural Objects at the CHP – Contributed by Francisca Ugalde and Cathy Faye.
A recent post by Brian Solis “The Curation Economy and the 3 C’s of Information Commerce” neatly deconstructed the information flow within the Social Network. The 3 C’s are creation, curation and consumption, and while consumption remains the largest activity he correctly identified curation as a vital part of the social information chain, as it is the intermediary and often principle connecting service between the authors and readers of content
There are many curation tools available (@williampearl Shirley Williams’ blog post references 40). Most serious Social Media participants use one or several of them to save interesting content discovered or referenced in their daily pursuit of engagement.
Though the name curation is applied to such tools as scoop.it list.ly Pinterest and others all too often these tools act as nothing more than scrapbooks, with photos and articles appended to pages because they caught our imagination, piqued our interest or satisfied our desire to be seen as a member of a community of interest.
It is true that many curating users perform a rudimentary evaluation to classify the curated content and to position it within a relevant category; an even smaller number provide some commentary on the content. But like a scrapbook these collections remain static with a last-in first-presented view of the collection that has been assembled. Content that was first collected generally remains buried under more recent entries, and interactive commentary is almost non existent. As a result the value of such collections is greatly diminished and the prime activity of social media curators appears to be browsing the curated pages of others in search of new content to display on their own.
This observation may be harsh, yet I believe that there are many curators who do far more than I have indicated here, however the current tools have limitations. Furthermore to raise curation to the level required to act as the intermediary between creation and consumption, as indicated by Brian Solis, we need to bring aspects of Information Lifecycle Management disciplines and processes to bear on the problem. In a previous post on the network weaver I had already identified curation as one of the 5 major components of the social networking architecture. It is notable that it takes up to 2 years for a post graduate to obtain an MFA in curatorial studies or a Curation Diploma from the British Museum. I have used the British Museum course curriculum as a basis for identifying the sub components of Social Media Information Curation.
Information Lifecycle Management concept applied to Social Media Curation
As can be seen from the diagram the information lifecyle has no end. Disposed (ie stored) information still needs to be maintained and re-evaluated and this is the task I have described as Collaborative Husbandry or collective farming. This is equivalent to the constant reexamination of requirements in The Open Group Architecture Framework (TOGAF), as current and new information can change curated landscape very quickly, and skilled curators should be able to adjust the curated content to accommodate this. The more sophisticated and comprehensive the collection the more curating resources are needed to maintain the information quality, which leads me to believe that enterprises will seek and appoint skilled curators and possibly even a Chief Curation Officer as they become increasingly dependent on external information and resources.
I would be interested to hear of additional requirements for Social Media Curation, as I believe we are still in discovery mode on what is needed to better identify, collect, discuss and exhibit the knowledge that is cascading through the global Social Media.
Related articles